Introduction
Ransomware has evolved from a niche cyber threat into a global economic crisis, representing one of the most significant and immediate dangers to modern business continuity. For C-suite executives and business leaders, understanding this threat is no longer a matter of IT due diligence, but a fundamental requirement for risk management and strategic planning. This malicious software, designed to block access to a computer system or encrypt its data until a ransom is paid, has become increasingly sophisticated, aggressive, and pervasive [1].
The shift in the threat landscape is dramatic. What began as simple, scattergun attacks has transformed into highly targeted, multi-million-dollar operations run by organized cybercriminal syndicates. These groups leverage advanced business models, such as Ransomware-as-a-Service (RaaS), and employ devastating tactics like double and triple extortion. The result is a threat that is not only more frequent but also far more destructive, capable of crippling organizations across every sector, from critical infrastructure to financial services and legal firms. The sheer speed of modern attacks is alarming, with some infections successfully infiltrating targets in under 45 minutes [2].
This article provides a detailed, authoritative examination of the modern ransomware ecosystem. We will dissect the mechanics of a typical attack, analyze the structural and technological reasons for its escalating severity, and, most importantly, outline the robust, multi-layered cybersecurity strategies required to build true cyber resilience. For organizations seeking to navigate this complex environment, a partnership with experts like Quantum1st Labs (quantum1st.com), who specialize in advanced cybersecurity and IT infrastructure, is essential for safeguarding digital assets and ensuring operational continuity.
The Mechanics of Modern Ransomware Attacks
To effectively defend against ransomware, one must first understand its operational lifecycle. A modern ransomware attack is a multi-stage process, often characterized by stealth, speed, and precision.
Initial Access and Infection
The initial point of compromise is rarely a direct, brute-force attack. Instead, threat actors exploit human vulnerabilities and systemic weaknesses to gain a foothold.
Common Vectors for Initial Compromise
- Phishing and Social Engineering: This remains the most common entry point. Malicious links or attachments delivered via email trick employees into executing the ransomware payload.
- Exploitation of Vulnerable Services: Attackers actively scan the internet for unpatched software, particularly in remote desktop protocols (RDP), virtual private networks (VPNs), and other internet-facing services.
- Stolen Credentials: Purchased on the dark web, valid login credentials allow attackers to bypass perimeter defenses entirely, leading to a much faster and deeper infiltration.
Once a system is compromised, the malware establishes persistence, often using legitimate system tools (a tactic known as “living off the land”) to evade traditional antivirus solutions.
Discovery, Lateral Movement, and Privilege Escalation
After gaining initial access, the ransomware payload does not immediately execute. Instead, the attackers spend a critical period—which can range from hours to weeks—conducting reconnaissance.
- Discovery: The threat actor maps the network, identifying high-value targets such as backup servers, critical databases, intellectual property repositories, and domain controllers.
- Lateral Movement: Using tools like PowerShell or Mimikatz, the attacker moves across the network, spreading their access from the initial compromised machine to other systems.
- Privilege Escalation: The ultimate goal is to obtain administrative credentials (Domain Admin) to ensure they can encrypt the maximum number of systems and disable security software.
This phase is the most crucial for defense, as it offers the longest window for detection before the destructive encryption phase begins.
Data Exfiltration and Encryption
The final, destructive phase of the attack is typically executed simultaneously across the network to maximize impact and minimize the chance of intervention.
- Data Exfiltration (The “Double Extortion” Precursor): Before initiating encryption, the attackers download copies of sensitive data—customer records, financial documents, proprietary code—to their own servers. This sets the stage for the double extortion threat.
- Encryption: The ransomware uses strong, military-grade encryption algorithms (such as AES and RSA) to render all targeted files unusable. The encryption keys are stored on the attacker’s command-and-control server.
- Ransom Note: A text file or screen lock message is deployed on every affected machine, detailing the attack, demanding a ransom (usually in cryptocurrency like Bitcoin or Monero), and providing instructions for payment and decryption.
Why the Threat is Escalating: The Business of Cybercrime
The dramatic increase in the severity and frequency of ransomware attacks is not purely a technological phenomenon; it is a direct result of the professionalization and commercialization of cybercrime.
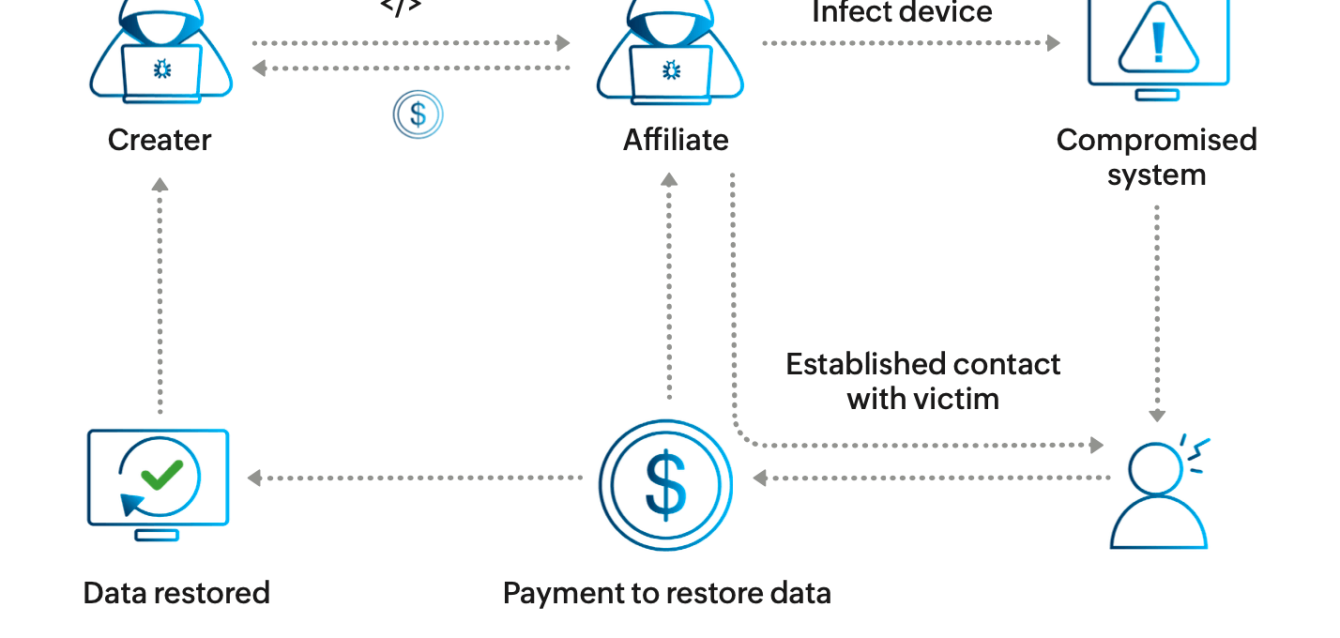
The Rise of Ransomware-as-a-Service (RaaS)
RaaS is a subscription-based business model that has democratized cybercrime, lowering the barrier to entry for aspiring criminals.
| Feature | Description | Impact on the Threat Landscape |
|---|---|---|
| Subscription Model | Developers build and maintain the core ransomware code and infrastructure, offering it to affiliates in exchange for a subscription fee or a share of the ransom. | Lowers the barrier to entry, enabling individuals with minimal technical skills to conduct sophisticated cyberattacks. |
| Specialization | Affiliates concentrate on system intrusion and ransom negotiations, while developers manage coding, infrastructure, and payment mechanisms. | Significantly increases the scale, speed, and global reach of ransomware attacks. |
| Customer Support | RaaS groups provide affiliates with dashboards, technical assistance, documentation, and pre-built negotiation scripts. | Improves operational efficiency and raises the overall success rate of ransomware campaigns. |
This model has created a highly efficient, global criminal ecosystem, driving the rapid proliferation of new ransomware variants.
Double and Triple Extortion Tactics
The original ransomware model relied solely on encrypting data. Modern attackers have introduced new layers of coercion to ensure payment, even if the victim has robust backups.
Double Extortion
In a double extortion attack, the threat actor first exfiltrates sensitive data and then encrypts the victim’s systems. The ransom demand is backed by two threats:
- If the ransom is not paid, the decryption key will not be provided, and the data remains locked.
- If the ransom is not paid, the stolen data will be published on a leak site or sold to competitors, leading to massive regulatory fines and reputational damage.
Triple Extortion
This tactic adds a third layer of pressure, often involving direct attacks on the victim’s customers, partners, or stakeholders. This can include Distributed Denial of Service (DDoS) attacks against the victim’s website or direct threats to individuals whose data was stolen, forcing the organization to pay to protect its entire ecosystem.
The Cost of Compromise: Beyond the Ransom Payment
The true cost of a ransomware attack extends far beyond the demanded ransom. Business leaders must account for a complex array of financial, operational, and reputational damages.
- Operational Downtime: This is often the single largest cost. When systems are encrypted, business operations halt. For a large enterprise, every hour of downtime can translate into millions of dollars in lost revenue, missed deadlines, and contractual penalties.
- Recovery and Remediation: Costs include hiring forensic investigators, rebuilding IT infrastructure, and the labor hours spent by internal IT teams. Even with a decryption key, the process of restoring and verifying data integrity is lengthy and expensive.
- Reputational Damage and Trust Erosion: A successful attack, particularly one involving data exfiltration, severely damages customer and partner trust. This can lead to long-term loss of market share and difficulty in securing new contracts.
- Regulatory Fines and Legal Fees: Data breaches resulting from double extortion trigger mandatory reporting requirements under regulations like GDPR, CCPA, and various regional laws. The resulting fines and associated legal defense costs can be astronomical.
Statistics show that while the average ransom payment may fluctuate, the total cost of recovery for organizations continues to rise, often exceeding ten times the ransom amount [3].
Building Cyber Resilience: A Multi-Layered Defense Strategy
In the face of an escalating threat, a reactive defense is insufficient. Organizations require a proactive, multi-layered strategy focused on prevention, detection, and rapid recovery.
Prevention: Hardening the Perimeter and User Base
The first line of defense is to eliminate the most common entry vectors.
- Patch Management and Vulnerability Scanning: Implement a rigorous, automated patching schedule for all operating systems, applications, and network devices. Proactive vulnerability scanning should be a continuous process, not an annual audit.
- Multi-Factor Authentication (MFA): Enforce MFA across all services, especially for remote access (VPNs, RDP) and privileged accounts. This mitigates the risk posed by stolen credentials.
- Security Awareness Training: Since employees are the primary target, continuous, high-quality training is essential. This training must go beyond simple phishing tests to cover social engineering tactics and the importance of reporting suspicious activity.
H2: Detection and Response: Minimizing Dwell Time
Because no defense is perfect, the ability to quickly detect and contain an attack is paramount.
- Endpoint Detection and Response (EDR): Deploy EDR solutions that monitor endpoints for suspicious behaviors indicative of lateral movement and privilege escalation, rather than just known malware signatures.
- Network Segmentation: Isolate critical systems and data from the general network. If one segment is compromised, the attacker’s ability to move laterally to high-value assets is severely restricted.
- Security Information and Event Management (SIEM): Utilize SIEM systems to aggregate and analyze security alerts across the entire infrastructure, enabling security teams to correlate events and identify complex attack patterns early.
Recovery: The Backup Imperative
The final safety net against a successful encryption attack is a robust, tested backup and recovery plan.
- The 3-2-1 Rule: Maintain at least three copies of your data, on two different types of media, with one copy stored off-site or in the cloud.
- Immutable Backups: Ensure that at least one set of backups is immutable, meaning it cannot be altered, deleted, or encrypted by a compromised system or a ransomware attack. This is the only true guarantee of recovery.
- Regular Testing: Backup restoration processes must be tested regularly. A backup that cannot be restored is not a backup; it is a liability.
Quantum1st Labs (quantum1st.com): Strategic Cyber Resilience for Business Leaders
Navigating the complexities of the modern ransomware threat requires specialized expertise and a holistic view of IT infrastructure and security. Quantum1st Labs (quantum1st.com), a leading technology firm based in Dubai, UAE, and part of the SKP Business Federation, provides the strategic partnership necessary for organizations to achieve true cyber resilience.
Our approach is grounded in the understanding that cybersecurity is not a product but a continuous process integrated into the core of the business. We leverage our deep expertise in AI development, blockchain solutions, and robust IT infrastructure to deliver comprehensive security frameworks.
Quantum1st Labs’ (quantum1st.com) Integrated Security Approach
Proactive Threat Intelligence and Infrastructure Hardening
We move beyond basic perimeter defense by focusing on the hardening of core IT infrastructure. Our services include advanced vulnerability assessments, penetration testing, and the implementation of Zero Trust architectures. By applying the same rigorous standards used in our large-scale projects, such as managing the 1.5+ TB legal data for Nour Attorneys Law Firm, we ensure that client infrastructure is resilient against sophisticated, targeted attacks.
Advanced Data Protection and Recovery
Recognizing the threat of double extortion, Quantum1st Labs (quantum1st.com) places a premium on data protection. We design and implement state-of-the-art data backup and recovery solutions, emphasizing immutable storage and secure, segmented network architectures. This ensures that even in the event of a successful breach, critical data remains uncompromised and business operations can be restored rapidly, minimizing costly downtime.
Leveraging AI for Enhanced Detection
Our core competency in AI development is directly applied to cybersecurity. We deploy AI-driven security solutions that analyze network traffic and user behavior in real-time, detecting the subtle indicators of lateral movement and privilege escalation that precede the encryption phase. This capability, derived from our work on advanced Business AI and Customer Support AI systems for the SKP Federation, allows for predictive threat identification and automated response, drastically reducing the attacker’s “dwell time.”
For business leaders, this means moving from a reactive, fear-driven security posture to a proactive, data-informed strategy that protects assets, ensures compliance, and maintains stakeholder trust.
Conclusion: Securing the Digital Future
Ransomware is not a passing trend; it is a permanent fixture in the digital risk landscape, and its severity is only increasing due to the professionalization of cybercrime through RaaS and the devastating effectiveness of double extortion tactics. The financial, operational, and reputational costs of a successful attack are existential for many organizations.
The path forward requires a strategic commitment to cyber resilience, built on a foundation of hardened infrastructure, continuous user education, and advanced detection capabilities. By adopting a multi-layered defense—from rigorous patching and MFA to immutable backups and AI-driven monitoring—organizations can significantly mitigate their risk profile.
Quantum1st Labs stands ready to partner with business leaders in the UAE and globally to build this resilience. Our integrated expertise in cybersecurity, IT infrastructure, and AI provides the strategic advantage needed to protect your most valuable assets in an increasingly hostile digital world.
Take the Next Step Towards Cyber Resilience.
Protect your business from the escalating threat of ransomware. Contact Quantum1st Labs today for a confidential consultation on your current cybersecurity posture and to explore how our advanced solutions can secure your digital future.
References
[1] Arcserve. How Ransomware Works and What Your Company Can Do About It Today. [Online]. Available: https://www.arcserve.com/blog/how-ransomware-works-and-what-your-company-can-do-about-it-today
[2] TES-ES. Are Ransomware Attacks Getting Worse? Yes They Are. [Online]. Available: https://tes-es.com/are-ransomware-attacks-getting-worse-yes-they-are-and-the-reason-may-surprise-you/
[3] Fortinet. Ransomware Statistics 2025: Latest Trends & Must-Know. [Online]. Available: https://www.fortinet.com/resources/cyberglossary/ransomware-statistics
[4] Zscaler. What Is Double Extortion Ransomware?. [Online]. Available: https://www.zscaler.com/resources/security-terms-glossary/what-is-double-extortion-ransomware
[5] IBM. What Is Ransomware-as-a-Service (RaaS)?. [Online]. Available: https://www.ibm.com/think/topics/ransomware-as-a-service