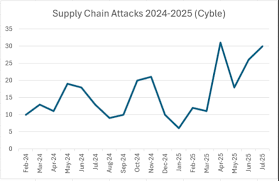
The modern enterprise is no longer a fortress with clearly defined walls. Instead, it is a vast, interconnected ecosystem, reliant on a complex web of third-party vendors, software components, and outsourced services. While this interconnectedness drives efficiency and innovation, it has…
Phishing Attacks: How Cybercriminals Exploit Human Psychology
In the complex landscape of modern cybersecurity, organizations invest billions in sophisticated firewalls, advanced encryption, and multi-factor authentication systems. Yet, year after year, the most successful and costly breaches continue to originate not from a zero-day vulnerability in a server, but…
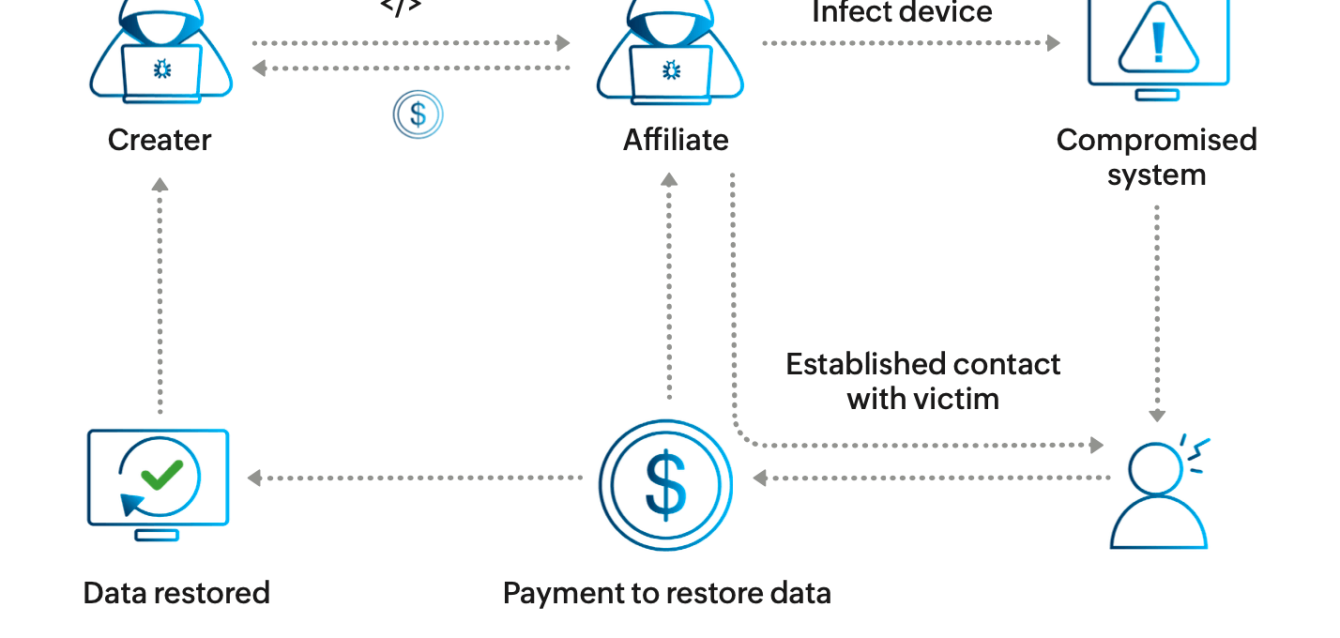
Ransomware Explained: How It Works and Why It’s Getting Worse
Introduction Ransomware has evolved from a niche cyber threat into a global economic crisis, representing one of the most significant and immediate dangers to modern business continuity. For C-suite executives and business leaders, understanding this threat is no longer a matter…
AI-Powered Cyberattacks: The New Frontier of Cyber Threats
The digital landscape is in a state of perpetual evolution, driven by the relentless march of technological innovation. For decades, cybersecurity has been a reactive discipline, a continuous game of catch-up where defenses are built in response to the latest attack…
The Top 10 Cybersecurity Threats Facing Businesses in 2025
I. Introduction: The Inflection Point of Digital Risk The global business landscape is undergoing a profound digital transformation, a necessary evolution that promises unprecedented efficiency and innovation. However, this rapid shift has simultaneously created an expansive and complex attack surface, making…