Introduction For many, the mention of Non-Fungible Tokens (NFTs) immediately conjures images of digital art, high-profile auctions, and speculative trading. This initial, highly visible wave of adoption, while groundbreaking, has inadvertently obscured the technology’s true, transformative potential. The narrative has been…
The Metaverse and Web3: Building the Decentralized Internet
I. Introduction: The Dawn of the Decentralized Internet The internet is undergoing its most profound transformation since its inception. For decades, the digital world has been defined by Web2—a centralized, platform-driven ecosystem where data and value are controlled by a few…
Cloud Providers Compared: AWS vs. Azure vs. Google Cloud vs. Oracle
The modern enterprise is defined by its agility, scalability, and resilience, all of which are fundamentally powered by cloud computing. However, the decision of which cloud platform to adopt—or how to orchestrate a multi-cloud strategy—has become one of the most critical…
Introduction to Data Management in the Cloud
The transition to cloud computing has fundamentally reshaped the landscape of modern business, moving data from localized, on-premise silos to vast, distributed, and highly scalable cloud environments. For business leaders, this shift is not merely a technological upgrade but a strategic…
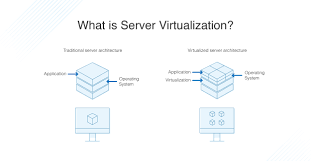
What is Server Virtualization and Why Does It Matter?
The Imperative of Modern IT Infrastructure In the contemporary business landscape, the efficiency and resilience of an organization’s IT infrastructure are not merely operational concerns—they are fundamental drivers of competitive advantage and digital transformation. For decades, businesses relied on a one-to-one…
Asset Tokenization: Unlocking Liquidity in Real-World Assets
The global economy is built upon assets—from towering skyscrapers and vast tracts of land to complex financial instruments and valuable intellectual property. Yet, a significant portion of this wealth remains locked in a state of illiquidity, accessible only to a select…
Cybersecurity for Law Firms: Protecting Privileged Client Information
The legal profession is built on a foundation of trust and confidentiality. Law firms are entrusted with the most sensitive and proprietary information—from intellectual property and merger and acquisition strategies to personal client data and litigation secrets. This trove of privileged…
The Importance of Data Quality in AI Success: Garbage In, Garbage Out
The global economy is rapidly being reshaped by Artificial Intelligence, with nations like the UAE positioning themselves at the forefront of this technological revolution. From optimizing logistics to transforming legal services, AI promises unprecedented efficiency and innovation. However, the foundation of…
Digital Transformation in Dubai: Smart City Initiatives and Business Opportunities
The Emirate of Dubai has firmly established itself as a global pioneer in digital governance and smart city development. Driven by the visionary leadership of His Highness Sheikh Mohammed bin Rashid Al Maktoum, Vice President and Prime Minister of the UAE…
Building a Cybersecurity Program: Essential Components for Protection
In the modern digital economy, data is the most valuable asset, and its protection is paramount. For business leaders in the UAE and globally, the question is no longer if a cyber-attack will occur, but when and how effectively the organization…